7 System-Level Security Risks in Institutional DeFi: From Order Flow to Governance
Risk does not sit inside one smart contract. It emerges from cross-layer interaction, incentive design, order flow power, and governance control.
Every week we hear about another institution entering DeFi: a new asset manager launching an on-chain strategy, a stablecoin issuer expanding into new markets, or an RWA platform bringing new forms of collateral on-chain.
The scale of capital being discussed is materially different from early DeFi cycles. It is larger, more structured, and measured in tens or hundreds of millions. However, the risk discussion often remains narrow. These are not “smart contract hack” scenarios, but structural risks embedded in the architecture you rely on.
Institutional DeFi exposure spans multiple interacting layers - regardless of whether the base layer is Ethereum, Solana, or another blockchain. The same structural dependencies exist:
Base Layer (L1): consensus, finality, and data availability
Execution Layers (L2s or appchains): high-throughput environments, often with privileged sequencing actors that determine order flow
DeFi protocols: DEX, lending markets, vaults, derivatives platforms
Bridges and cross-chain routers: asset transfers and message passing between domains
Oracles: external data feeds used for pricing, collateral valuation, and liquidations
Governance systems: multisigs, upgrade keys, parameter control, emergency functions
Allocating capital into DeFi means relying on the integrity, coordination, and economic stability of all these layers simultaneously. Risk does not sit inside one smart contract.
It emerges from cross-layer interaction, incentive design, order flow power, and governance control.
The rest of this article breaks down the major system-level risks institutional capital must explicitly model before scaling on-chain exposure.
1. Settlement Layer Risk (Base-Layer Dependence)
Whether you deploy on Ethereum, Solana, or another public blockchain, institutional exposure ultimately depends on the properties of the base settlement layer. Rollups (L2 blockchains) inherit security and finality from an underlying consensus system. Institutional exposure, therefore depends on:
Honest-majority consensus assumptions
Deterministic finality guarantees (when your transaction becomes irreversible from the blockchain ledger)
Network congestion behavior
Fee market dynamics under stress
If the base layer becomes congested or unstable, cross-layer settlement slows down. Exit paths become delayed. Forced liquidations may executed at unfavorable times.
History provides clear examples. During periods of extreme NFT minting activity, gas fees on Ethereum spiked to thousands of dollars per transaction. In 2022, the Yuga Labs Otherside mint led to severe congestion and transaction failures across the network. On Solana, extremely high transaction numbers caused the blockchain to halt its functioning entirely for even 6 hours!
For retail participants this is inconvenient.
For institutions, this becomes a redemption timing and liquidity risk.
2. Order Flow and MEV (Execution Asymmetry)
Blockchains do not guarantee neutral execution. Whether on Ethereum, Solana, or private networks, transactions typically pass through a mempool before being included in a block.
A mempool is a waiting area for pending transactions. On networks like Ethereum, this pool is visible to everyone. This creates transparency, but also strategic vulnerability. Large trades, liquidations, or redemptions can be anticipated and economically exploited before confirmation. For institutional-sized transactions, this becomes material.
If a transaction is visible before execution, it can be:
Copied
Reordered
Sandwiched
Backrun
Used as input for arbitrage
This is the foundation of what is commonly referred to as MEV (Maximal Extractable Value).
Ethereum has evolved toward architectures such as proposer-builder separation (PBS), where block construction and block proposal are separated. This improves specialization and market efficiency.
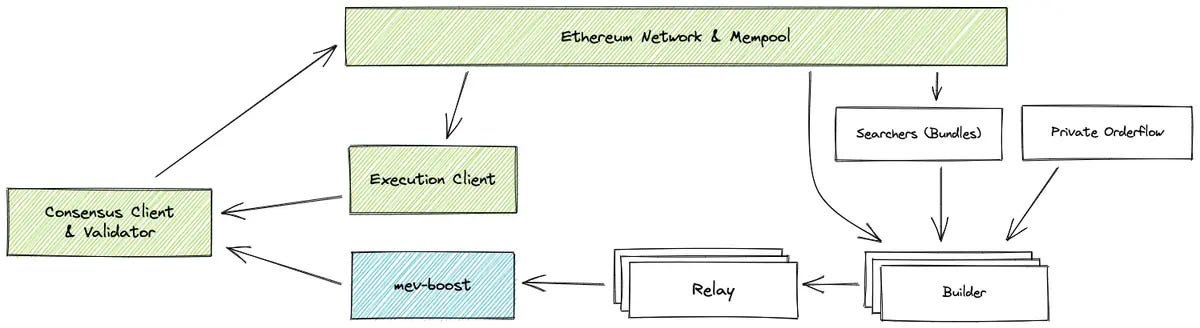
This setup allows transactions to be submitted through private relay systems rather than the public mempool. These systems forward transactions directly to block builders. In this model:
The transaction is not publicly visible before execution
It becomes visible only once included in a block
For institutions, private submission is often a minimum requirement for large trades.
Some forms of arbitrage and liquidation are necessary for DeFi to function efficiently. They maintain price alignment and solvency. The existence of MEV is not inherently problematic. The risk arises when execution asymmetry is unmodeled, unpriced, or misunderstood.
This is not a “hack” scenario.
It is a structural execution risk embedded in how transactions are observed, ordered, and finalized.
3. Liquidity Fragmentation Risk
Liquidity in DeFi is not unified. It is fragmented across L1, multiple L2s, application-specific chains or isolated lending pools and vaults For institutions, this fragmentation creates three structural problems:
Capital inefficiency – Liquidity must be deployed across multiple venues to access opportunity.
Slippage under size – Large trades move markets, especially in fragmented pools.
Yield compression – In lending markets and vaults, APY is directly dependent on utilization. The more capital you deploy, the lower your marginal yield.
Most yield dashboards and aggregators do not model capital impact. They show static APY, not marginal APY under institutional size.
On the trading side, slippage and MEV risks increase with order size. Solver-based execution systems such as CoW-style batch auctions or intent-based routing can mitigate some of this, but fragmentation remains structural.
During stress events, liquidity can evaporate quickly. Institutions discover that quoted liquidity and executable liquidity are not the same.
Fragmentation creates hidden opportunity cost and exit friction.
4. Oracle and Valuation Risk
Tokenized RWAs and lending markets rely on external price feeds.
Even robust oracle systems are exposed to:
Short-term manipulation within deviation thresholds
Latency between market moves and on-chain updates
Liquidity-dependent pricing distortions
In leveraged systems, small distortions can trigger:
Forced liquidations
Liquidation cascades
Stablecoin supply contraction
Oracle risk is rarely binary. It does not require full oracle failure.
It only requires temporary distortion within accepted parameters.
For institutions deploying leveraged or collateralized structures, this becomes a solvency modeling issue.
5. Governance and Upgrade Risk
Protocols evolve. Governance can:
Modify collateral factors
Adjust liquidation thresholds
Change interest-rate curves
Upgrade smart contracts
Pause critical functionality
From an institutional perspective, this represents embedded counterparty exposure.
Even if governance is non-malicious, parameter changes during stress can materially affect positions. Emergency pauses can lock liquidity. Upgrade risk introduces execution uncertainty.
Institutional allocation requires explicit modeling of who controls upgrade keys, how governance decisions are made, and what the response time is under crisis.
6. Cross-Domain Settlement and Bridge Risk
Tokenized RWAs and stablecoins increasingly operate across multiple domains:
L1 ↔ L2
L2 ↔ L2
Rollup ↔ appchain
On-chain ↔ off-chain systems
Each bridge introduces:
Proof verification assumptions
Message finalization delays
Data availability dependencies
Cross-domain settlement risk is frequently underestimated in institutional models.
Exit timing, redemption flows, and liquidity routing depend on bridge finality and liveness guarantees.
Institutions must ask:
What is the worst-case withdrawal time?
What happens under sequencer halt?
What if data availability is temporarily disrupted?
Bridge architecture is not just a technical concern. It is a capital mobility constraint.
7. Liquidity Shock and Forced Liquidation Spiral Risk
The most misunderstood risk is systemic liquidity spiral risk.
Under stress:
Prices decline
Liquidations trigger
Liquidity thins
Slippage increases
Additional liquidations trigger
On rollups, sequencing power and latency amplify this dynamic. Liquidations may cluster within short windows. Market depth may not absorb forced selling.
For RWA issuers and stablecoin systems, this can lead to:
Temporary depegs
Redemption bottlenecks
Yield collapse
Capital flight
This is not a protocol bug.
It is an equilibrium outcome under stressed liquidity and leverage conditions.
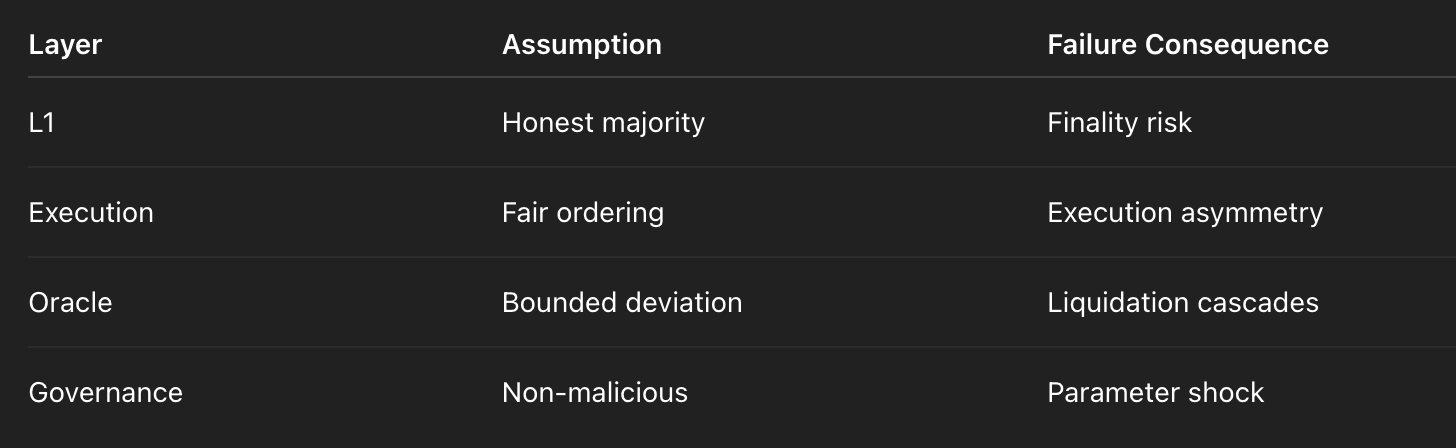
Explicit Trust Assumptions
Every institutional deployment implicitly assumes:
The base blockchain layer operates under honest-majority consensus
Transactions (from mempool) are ordered fairly for execution
Data availability mechanisms function within bounds
Governance keys are not malicious or compromised
Oracles remain within bounded manipulation thresholds
The issue is not that these assumptions exist.
The issue is when they are not written down and stress-tested.
Closing Thoughts
Institutional DeFi risk is not protocol-specific. It is architectural. The seven risk domains discussed above share a common feature: they emerge from the interaction of consensus, execution, liquidity, governance, and cross-domain settlement.
A protocol audit tests code.
A yield dashboard shows returns.
Neither models structural exposure.
An institutional-grade framework must explicitly document:
Settlement assumptions at the base blockchain layer
Order flow control
Liquidity depth under institutional size
Governance authority and upgrade rights
Cross-domain exit guarantees
Without this, exposure remains implicit. Institutions that formalize these assumptions deploy capital with structural clarity. The next phase of institutional DeFi will not be defined by innovation alone. It will be defined by better risk architecture.
If this framework is relevant to your DeFi allocation, RWA issuance, I am happy to discuss how to operationalize it.

